HIPAA Security Rules
De-Identifying Protected Health Information
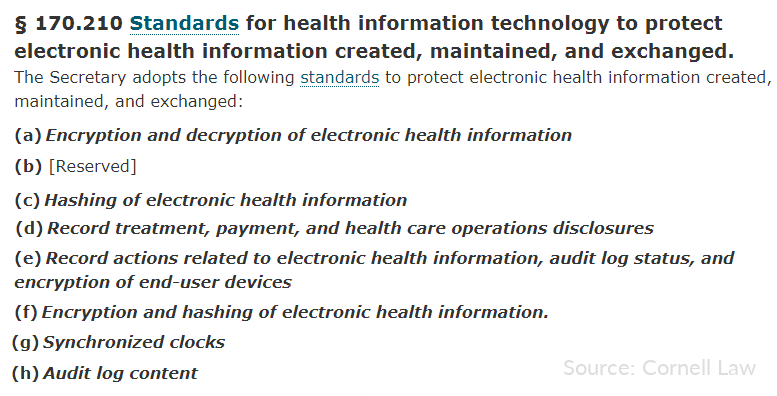
To safeguard Protected Health Information (PHI) subject to the HIPAA Safe Harbor Security rule, regulations like 45 CFR 164.312 and 170.210 specify encryption or hashing of 18 key identifiers. IRI software supports this rule with those and other PHI-obfuscating functions.
More specifically, built-in data discovery, classification and masking functions in the IRI FieldShield, DarkShield, and CellShield products -- or the IRI Voracity platform which includes them -- help you find, catalog, and de-identify PHI in structured and unstructured data sources automatically. These include RDBs, flat files, NoSQL DBs, Excel, PDF and Word, HL7, X12 and FHIR EDI files, DICOM and other image file formats.
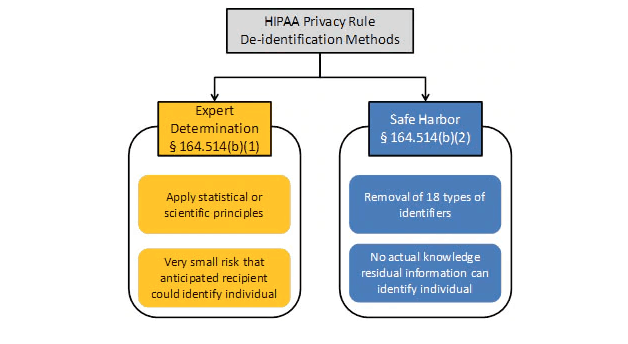
Alternatively, the HIPAA Expert Determination Method Rule, allows compliance through certified mitigation of re-identification risk. Integrated re-ID risk scoring and anonymization technology in IRI software statistically measures that risk, and blurs quasi-identifiers to comply with this rule, too.
Learn more about HIPAA-mandated de-identification and IRI solutions for it
De-identification refers to processes that disassociate personally identifiable information (PII) within protected health information (PHI) repositories and other "data at risk."
PHI de-identification is a specific requirement in the healthcare industry, where for example, it is used in both "safe harbor" and "expert determination method" practices in medical research (to remove patient identities from study models). De-identification is also a blanket term referring to the anonymization or masking of PII in many other industries.
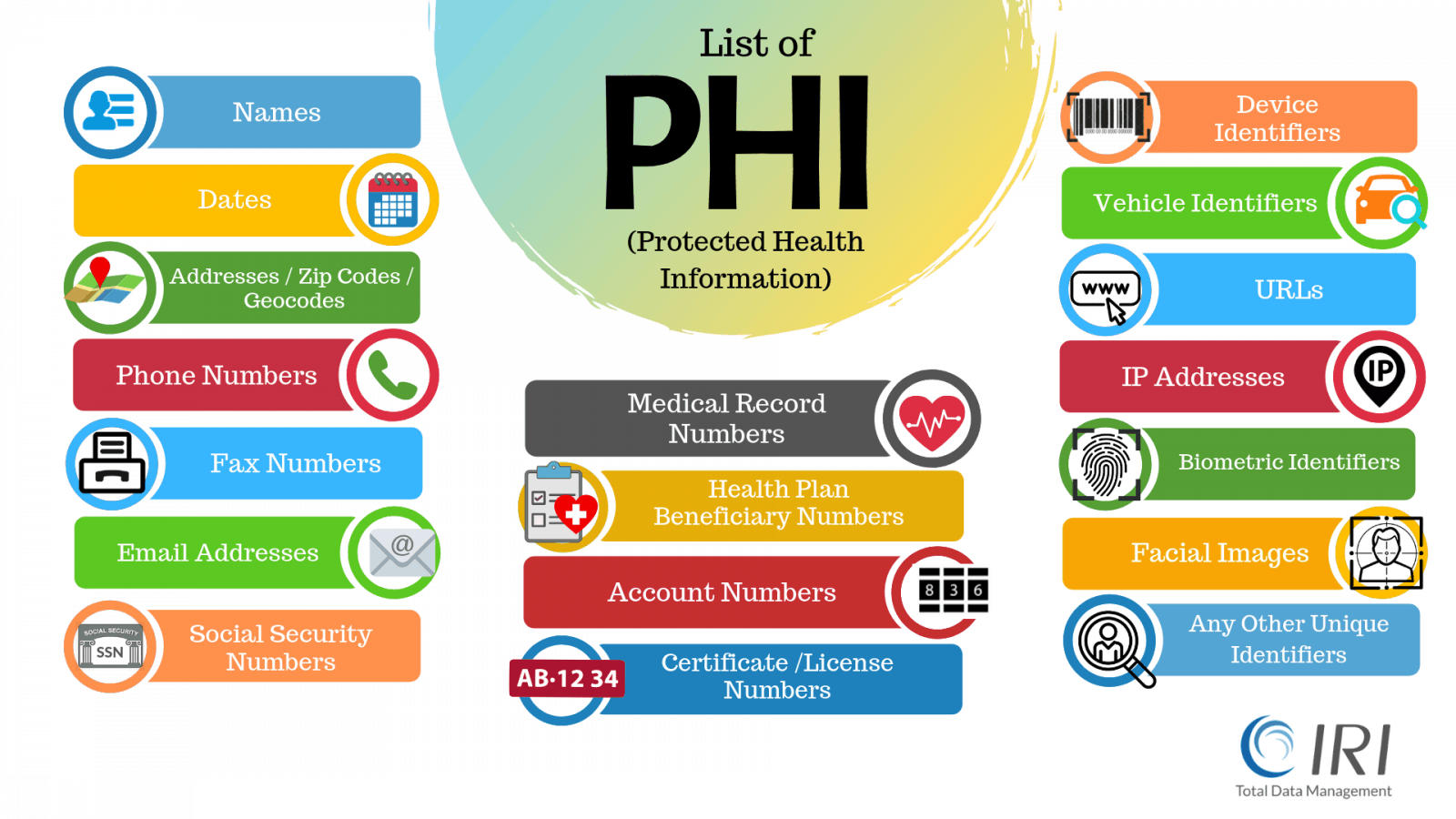
The most recent Security Rule in HIPAA regulations (45 CFR Parts 160 and 164) spell out the compliance requirements for those entities managing PHI. HIPAA rules apply to 18 specific identifiers:
|
Name |
Address |
Birthdate |
|
Phone # |
Fax # |
Email Address |
|
Social Security # |
Medical Record # |
Health Insurance Beneficiary # |
|
Account # |
Certificate # |
Vehicle ID # |
|
Device ID # |
Personal URL |
IP Address |
|
Biometric ID |
Facial Image |
Other Unique ID Code |
Each of the data masking software products in the IRI Data Protector suite helps you find and classify, and then protect PII, PAN, PHI, etc. in multiple data sources for Safe Harbor rule compliance. They also work hand-in-hand with free, advanced re-ID risk scoring technology for compliance with the Expert Determination Method rule. See this article in HIPAA Journal for more information about what constitutes PHI.
HIPAA compliance requires either:
Redaction - Safe Harbour
Manipulating, masking, or removing these key identifiers so that it is difficult or impossible to identify an individual or restore the original data.
De-Identification - Expert Determination Method
Stripping the identifiers, and generalizing quasi-identifiers until an expert determines the statistical risk of re-identification is very low.
HIPAA Data Compliance Course
Learn More about a three-hour online course covering de-identification and risk scoring processes on structured PHI data. It also includes sessions related to compliance certification, breach insurance, and breach claim defense.
Blog Article
Other Resources