Data-Centric Security
Data Masking
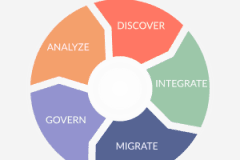
Find and Fix Data at Risk
Classify PII centrally, find it globally, and mask it automatically. Preserve realism and referential integrity using encryption, pseudonymization, redaction, and other rules for production and test envrionments.
Learn more
Comply with Data Privacy Laws
Delete, deliver, or anonymize data subject to CIPSEA, DPA, FERPA, GDPR, GLBA, HIPAA, PCI, POPI, etc. Verify compliance via human- and machine-readable search reports, job audit logs, and re-identification risk scores.
Learn more
Protect Data throughout its Lifecycle
Optionally mask data as you map it. Apply FieldShield functions in IRI Voracity ETL, federation, migration, replication, subsetting, or analytic jobs. Or, run FieldShield from Actifio or Commvault jobs to mask DB clones.
Learn more
References
FieldShield Use Cases

Payment Card Industry Data (PCI)
"FieldShield decrypts and re-encrypts fields in our credit card migration and test sources, and easily generates and manages encryption keys."
Protected Health Information (PHI)
"We continue to rely on FieldShield for flat-file and DB de-identification in order to comply with government healthcare privacy regulations."

Personally Identifiable Information (PII)
"We use FieldShield to anonymize HR data in complex file feeds, to segment and substitute values based on field-level conditions."
Do You Need FieldShield?
Take the FieldShield Quiz
- Do you collect or process PII or other "data at risk"? Do you know where (all of) it is?
- Is that data safe from a breach; i.e., could it be used were it stolen or exposed?
- Does your department comply with data privacy regulations? Can you prove it?
- Do you use multiple tools or methods to protect different DB columns in different ways?
- Can you protect only the data at risk, so you can see and use the non-sensitive data?
- Does your masked data look real enough? Is it referentially correct?
- Can you score your masked data sets for re-ID risk and anonymize quasi-identifers?
- Does it take too long to learn, implement, modify, or optimize your data masking jobs?
- Can you mask data in your ETL, subsetting, migration/replication, CDC or reporting tasks?
Complete Data Masking
Every Source:
Flat Files
RDB & NoSQL DBs
Semi-structured Files
Mainframe & Index Files
S3, HDFS, MQTT & Kafka
Pipes, Procedures & URLs
Excel Spreadsheets (CellShield)
Unstructured Files & Faces (DarkShield)
Every Protection:
Blur or Bucket
Bit Shift/Scramble
Encrypt & Decrypt
Encode & Decode
Delete or Redact
Hash or Tokenize
Pseudonymize & Restore
Random Generate or Select
Custom (New Field) Functions
Every Deployment:
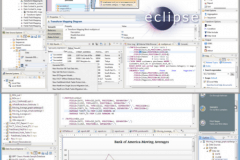
Eclipse IDE
Command Line
Batch/Shell Scripts
Ad Hoc or Scheduled
In-situ/SQL Procedures
System/API Library Calls
Replication, Test & DevOps
Incremental Update/Refresh
IRI Defines Startpoint Security | Outlook Series
Listen now here.
Learn more about FieldShield
Data Masking White Paper
Download now.
What Others Are Reading

Data Masking vs. Data Encryption
Do you know the differences between them? Learn about these two popular forms of data obfuscation and when to use them.

Which Masking Function is Best?
Read this review of the important decision criteria, including realism, reversibility, consistency, speed, and security.

PCI Tokenization in FieldShield
The Payment Card Industry Data Security Standard, or PCI DSS, requires encryption or tokenization of primary account numbers.